Recently, I took a Raspberry Pi I had lying around (who doesn’t?) and decided to install Pi-Hole.
Pi-Hole is essentially a DNS server for your home, running on a Raspberry Pi. It’s job is to filter DNS requests to the internet so that advertising domains are blocked - thus reducing your traffic, and blocking pesky ads. I won’t cover the install, since it’s posted in numerous places, but essentially, I installed Raspbian on an SD card, and inserted the SD card. SSH’d into the Raspberry pi, and ran the command to install Pi-Hole.
After the install was complete, I had about 150k domains on the blocklist out of the box. Additionally, I setup DNS forwarding to OpenDNS as my upstream DNS servers to block additional content types.
Homelab DNS resolution
Pi-Hole was setup as 192.168.1.2, and I edited my DHCP server (my gateway) to hand out that address to all clients. Now, since I run a homelab, I needed a way to have tsmith.local sent to my homelab DCs - so, another SSH session into the Raspberry Pi to enable DNS requests to that domain to be forwarded to the domain DCs, and not on out the internet.
I created a new file " 02- tsmith .local.conf" in /etc/dnsmasq.d/
server=/tsmith.local/192.168.2.11 server=/tsmith.local/192.168.2.12
After I saved the file, I went into Pi-Hole administration to restart dnsmasq (under settings / system) and voila! I could now resolve any host on the homelab domain.
Additional Blocklists
There are many blocklists available on the internet to use, and essentially, they are all just giant text files that someone (hopefully) maintains properly.
In the Pi-Hole administration page, I went to Settings / Blocklists and added some more.
First, I went to https://firebog.net and used every list with a checkmark beside it. That indicated those lists are least likely to interfere with web browsing. Next, I went to the Blocked List Project https://tspprs.com/ and used the Combined List. The combined list has since been retired, and the new URL is at blocklist.site/app
This took my total blocked domains to 1,402,431 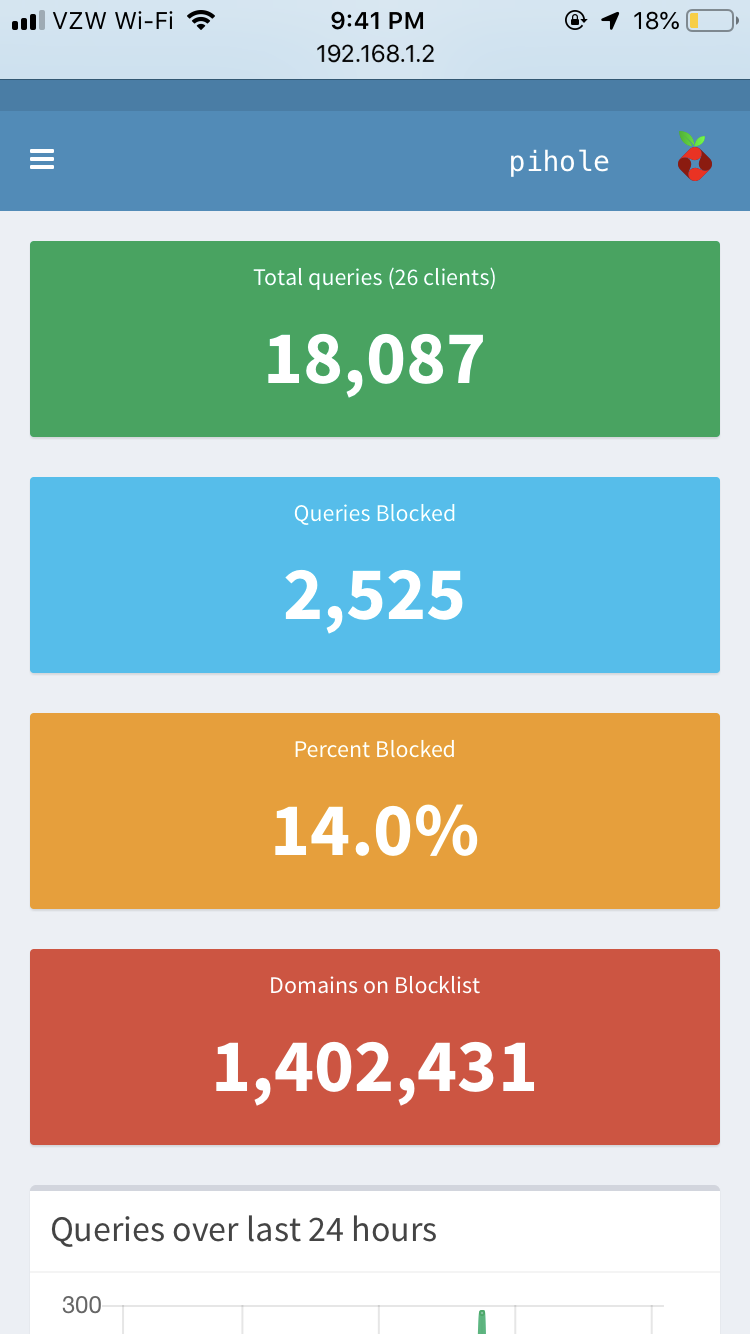
Lists
Here are the lists I currently use on my pi-hole:
https://raw.githubusercontent.com/StevenBlack/hosts/master/hosts https://mirror1.malwaredomains.com/files/justdomains http://sysctl.org/cameleon/hosts https://zeustracker.abuse.ch/blocklist.php?download=domainblocklist https://s3.amazonaws.com/lists.disconnect.me/simple _tracking.txt https://s3.amazonaws.com/lists.disconnect.me/simple _ad.txt https://hosts-file.net/ad _servers.txt https://adaway.org/hosts.txt https://v.firebog.net/hosts/AdguardDNS.txt https://raw.githubusercontent.com/anudeepND/blacklist/master/adservers.txt https://v.firebog.net/hosts/Easylist.txt https://pgl.yoyo.org/adservers/serverlist.php?hostformat=hosts;showintro=0 https://raw.githubusercontent.com/StevenBlack/hosts/master/data/UncheckyAds/hosts https://www.squidblacklist.org/downloads/dg-ads.acl https://hosts-file.net/grm.txt https://reddestdream.github.io/Projects/MinimalHosts/etc/MinimalHostsBlocker/minimalhosts https://raw.githubusercontent.com/StevenBlack/hosts/master/data/KADhosts/hosts https://raw.githubusercontent.com/StevenBlack/hosts/master/data/add.Spam/hosts https://v.firebog.net/hosts/static/w3kbl.txt https://v.firebog.net/hosts/Easyprivacy.txt https://v.firebog.net/hosts/Prigent-Ads.txt https://gitlab.com/quidsup/notrack-blocklists/raw/master/notrack-blocklist.txt https://raw.githubusercontent.com/StevenBlack/hosts/master/data/add.2o7Net/hosts https://raw.githubusercontent.com/crazy-max/WindowsSpyBlocker/master/data/hosts/spy.txt https://s3.amazonaws.com/lists.disconnect.me/simple _malvertising.txt https://hosts-file.net/exp.txt https://hosts-file.net/emd.txt https://hosts-file.net/psh.txt https://mirror.cedia.org.ec/malwaredomains/immortal _domains.txt https://www.malwaredomainlist.com/hostslist/hosts.txt https://bitbucket.org/ethanr/dns-blacklists/raw/8575c9f96e5b4a1308f2f12394abd86d0927a4a0/bad _lists/Mandiant_APT1_Report_Appendix_D.txt https://v.firebog.net/hosts/Prigent-Malware.txt https://v.firebog.net/hosts/Prigent-Phishing.txt https://gitlab.com/quidsup/notrack-blocklists/raw/master/notrack-malware.txt https://ransomwaretracker.abuse.ch/downloads/RW _DOMBL.txt https://ransomwaretracker.abuse.ch/downloads/CW _C2_DOMBL.txt https://ransomwaretracker.abuse.ch/downloads/LY _C2_DOMBL.txt https://ransomwaretracker.abuse.ch/downloads/TC _C2_DOMBL.txt https://ransomwaretracker.abuse.ch/downloads/TL _C2_DOMBL.txt https://v.firebog.net/hosts/Shalla-mal.txt https://raw.githubusercontent.com/StevenBlack/hosts/master/data/add.Risk/hosts https://www.squidblacklist.org/downloads/dg-malicious.acl https://tspprs.com/dl/cl1 ****
\\\\ See updated lists at blocklist.site/app