Recently, I had a question about using a managed service account for Veeam’s Backup for Office 365, so I thought I would write about how to setup a managed service account, and switch services over to that account.
If you aren’t aware, managed service accounts exist in newer window’s domains. The account’s password is managed by Active Directory and the server allowed to use it, and is changed regularly, while us human’s have no way to access the password.
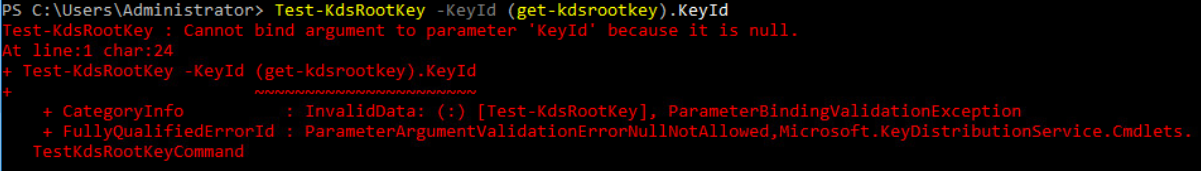
Since I haven’t used managed service accounts in my domain yet, I had to create a key. I verified first that the key did not exist.
test-kdsrootkey -keyid (get-kdsrootkey).keyid
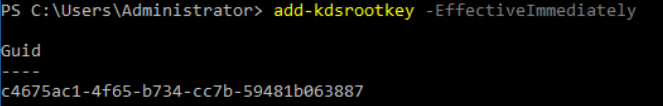
add-kdsrootkey -effectiveimediatly
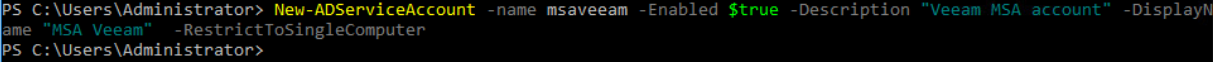
Now that I have a key, it’s time to create a new service account. This isn’t done in the gui, but in powershell on a domain controller.
Below is the command to create a new account named “msaveeam” with a description “Veeam MSA account” and a display name of “MSA Veeam”.
new-adserviceaccount -name msaveeam -enabled $true -description “Veeam MSA account” -displayname “MSA Veeam” -RestrictToSingleComputer
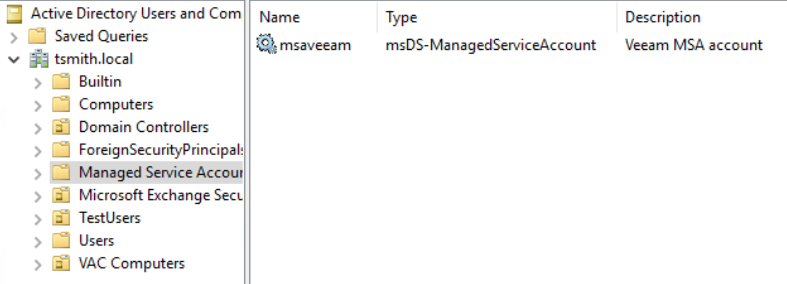
Now, in the OU Managed Service Accounts, you can see the newly created account.
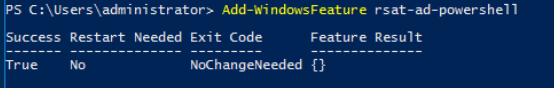
Next, it’s time to switch over to the guest server, which will consume the account. First, we need to install the remote server admin powershell for AD.
add-WindowsFeature rsat-ad-powershell
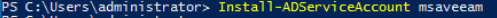
Then, run the powershell command to enable this server to use the managed service account.
Install-ADServiceAccount msaveeam
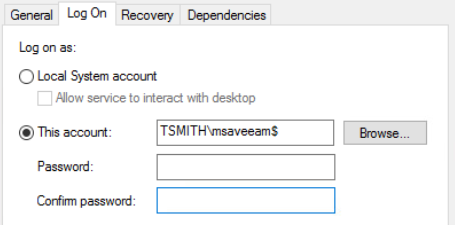
Now, let’s go into Services, and change the Veeam services to use the new account. When adding the account, make sure both password fields are blank.
Since I’m using this account for the Veeam Backup for Office 365 software, I also needed to edit my backup jobs and re-enter the o365 credentials int he jobs, as this new service account couldn’t decrypt the saved credentials.
MSAs (managed service accounts) are a great resource for AD environments since they can meet the requirement of complex, changing passwords, without the overhead of a user logging into each server to change the passwords.