Veeam has always been a great product for backup and replication, and in the recent past, they had introduced Cloud Connect, as a way to have integrated offsite backups to a hosted provider. What makes Cloud Connect really special, is that all communication to the cloud provider is over a single port. No need for VPNs or advanced networking.
There are many Cloud Connect providers as well, all competing for your business. Some offer just basic storage offsite, while others offer redundant storage replicated to another geographic region.
Also, Cloud Connect Enterprise is available, providing the Enterprise datacenter to have Cloud Connect internally, as a way to manage remote Veeam Installs as well as their offsite backups back to a central location.
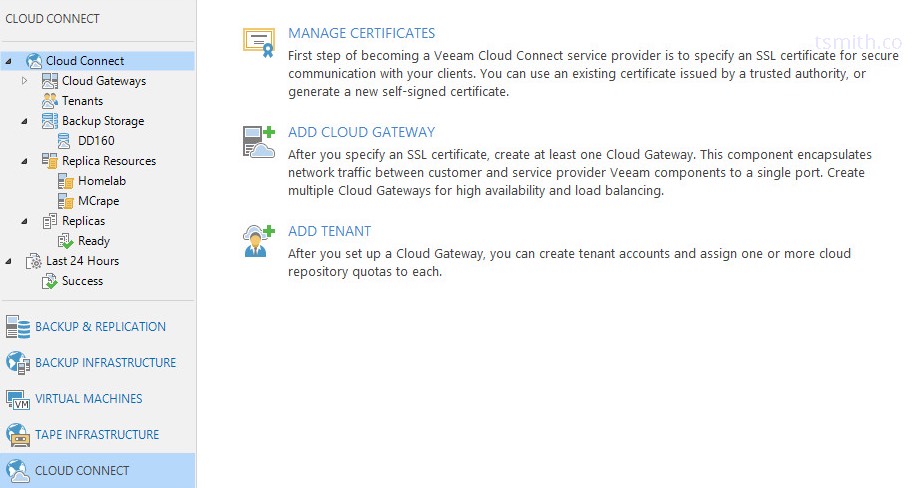
So, Let’s get started with the setup on the Service Provider side of things! First thing’s first - you’ll need a valid license key to unlock the Cloud Connect capabilities. I’ll assume installing Veeam Backup and Replication is not an issue, or it has already been installed. Once the Veeam license is applied, the Cloud Connect area will now show up on the left-hand side.
Prerequisites:
Before we can get starting, let’s get some things setup first. Veeam Backup and Replication is installed and licensed, so we can check that off the list. Next, we will need a Repository configured under Backup Infrastructure, so we can present that storage to the Cloud Connect clients. In my case, I have a Data Domain setup using DD Boost. In my lab, I’m using the VBR server for all the roles. However, in a real-world deployment, we would want to have some other Windows VMs spun up to handle the roles of Cloud Gateway and WAN Accelerator. Be sure to add the WAN Accelerator role to a VM under Backup Infrastructure and configure for heavy use. The WAN Acceleration page from the Veeam Best Practices guide has some excellent info on the subject.
Configuration:
Certificates:
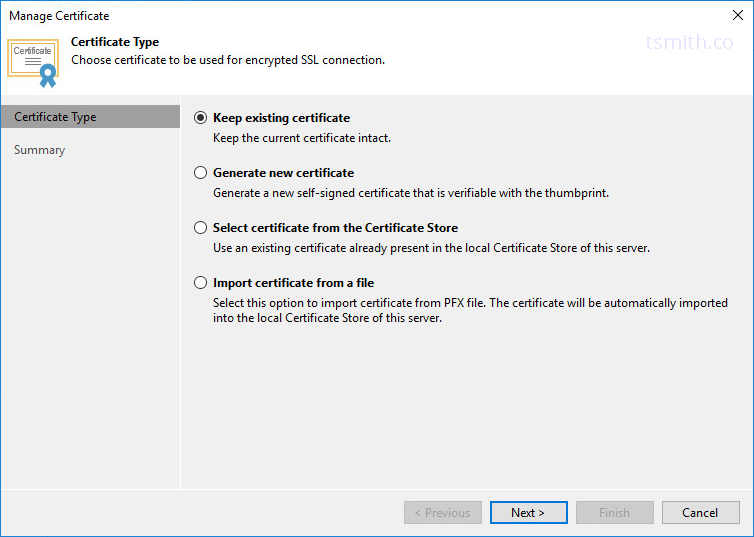
Veeam Cloud Connect uses encryption to get the data between sites. (In fact, in any Veeam environment, if Veeam detects that the non-private IP ranges are used, it automatically encrypts backup traffic across that link!) To setup the Encryption, we will want to import a valid SSL certificate that has been signed by a trusted authority. In this lab environment, I’m simply going to choose the option to use a self-signed certificate, which Veeam can generate. Luca Dell’Oca also recently published a great post on using Let’s Encrypt with Veeam .
Cloud Gateway:
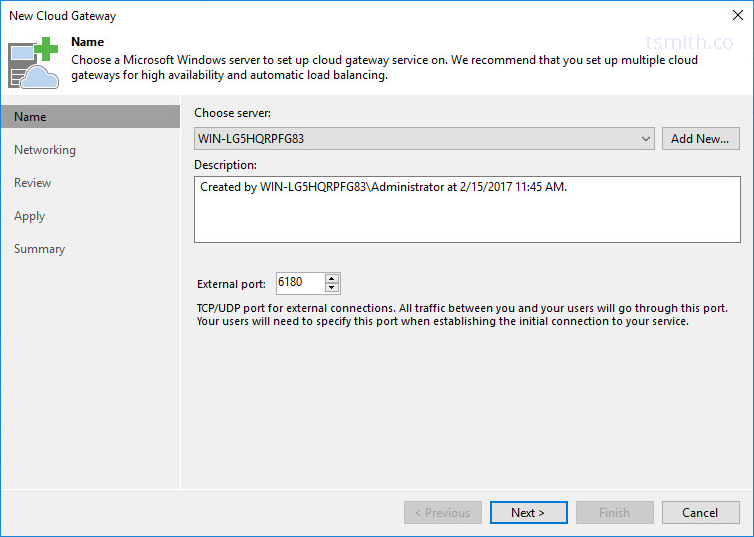
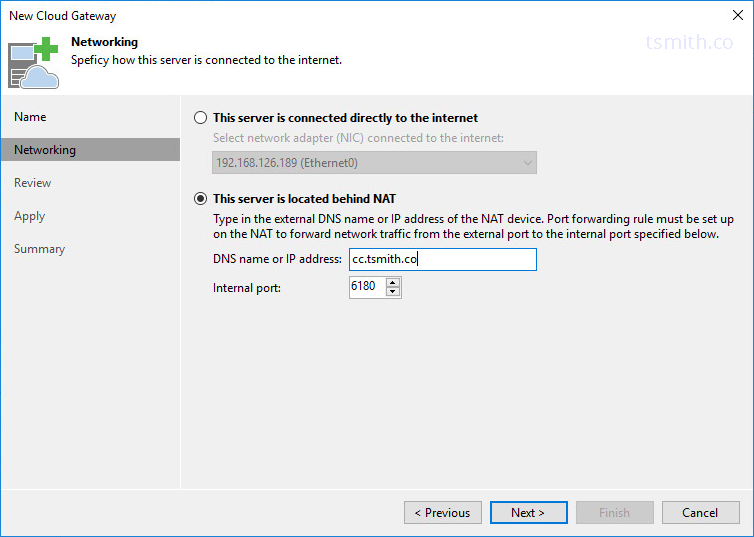
Next up is configuring a Cloud Gateway. This role is what the client will communicate to from the outside world. Our Cloud Gateway(s) typically will be separate VMs that either have a WAN IP assigned to them, or are behind NAT with TCP port 6180 passed through to them. All the clients will use TCP 6180 to connect to the gateway and pass all it’s backup traffic through into the Repository space assigned.
Like many other Veeam roles, we will want to first add the server as a managed Windows server into the Veeam console, and then we can select it for the Cloud Gateway role.
In my lab, the Cloud Gateway is behind NAT, and I have 6180 translated in, so I selected the appropriate option. Be sure to have a valid DNS name for clients to connect to. While IP is an option, if for some reason your IP changes, you would have to update all the clients, instead of just an A record in DNS.
Tenants:
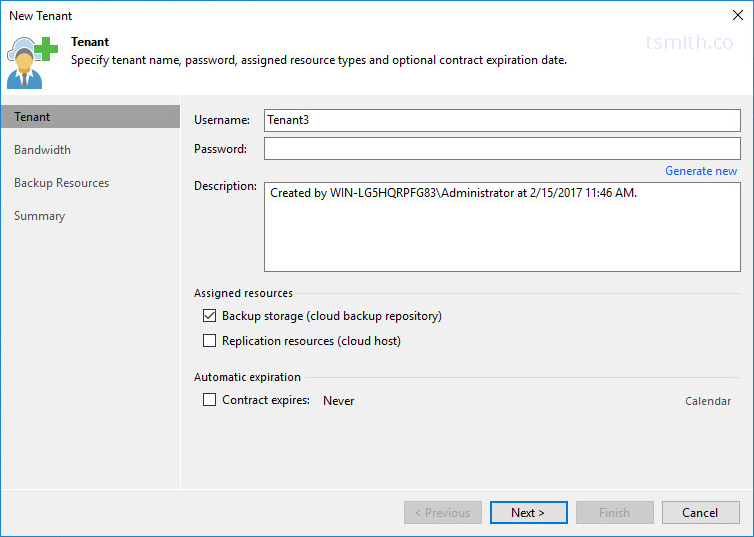
Now that we have the underlying infrastructure in place (Veeam, Repository, Cloud Gateway) it’s time to setup some tenants. A Tenant can be setup with sub-tenants as well, however, we won’t be covering that in this post. In the navigation tree, select Tenants, and create a new Tenant. Assign a username and a strong password, or allow Veeam to generate a new password for you.
Choose “Backup Storage” under assigned resources. This will allow a cloud repository to show under the tenant’s Veeam console once they authenticate. The other option, “Replication Resources” is for cloud providers who allow Veeam to replicate into their environment, providing a full DR site, where virtual machines can be spun up in a disaster scenario.
Last, you can choose if this agreement with the Tenant expires at a certain point, or leave unchecked for it to never expire.
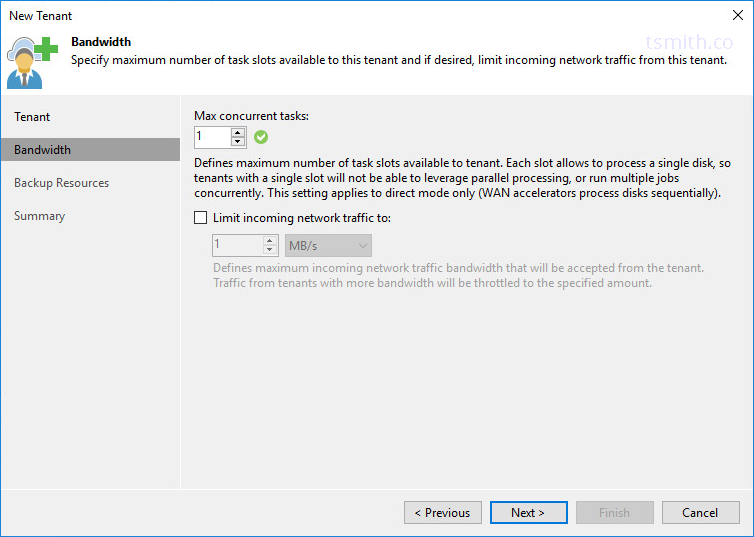
Next, we can choose what types of limitation we have in place for this tenant. For maximum concurrent tasks, this value will vary depending on whether or not WAN Accelerators will be in use. As the description shows, WAN Accelerators will handle disks sequentially, while not using them will allow disks to process in parallel.
Be sure to setup bandwidth limitations for each Tenant as well, which will prevent one tenant from overwhelming the pipe, and possibly affecting the speeds of other tenants.
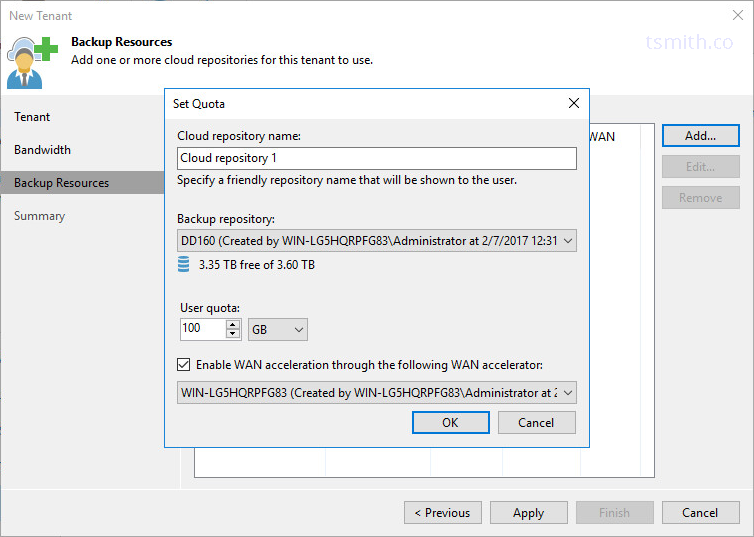
Last, we want to assign the Backup Repository to the Tenant. The Cloud Repository Name, is the name that will show in the Tenant’s VBR console, so be sure to name appropriately. Then, select what physical repository will be used, and how much that Tenant is allowed to consume of it. Some providers will want to present multiple repositories to their Tenants, such as a deduped repository, or one backed by different RAID levels or protection methods.
Finally, we are going to use our Wan Accelerator that we setup as a prerequisite. With Veeam, the WAN accelerator allows for reduced WAN traffic, as redundant blocks are not copied across the link, since they already exist in the cache on the accelerator. If the tenant is licensed for WAN acceleration, 99% of the time, it will be beneficial to use.
Final thoughts
At this point, the tenant can now connect and start sending backup data to the cloud environment. Continue creating additional tenants in the same manner. When acting as a service provider, you will want to verify capacities. Repository capacity, Bandwidth capacity, and also the capacity of disk space assigned to the WAN Accelerators.
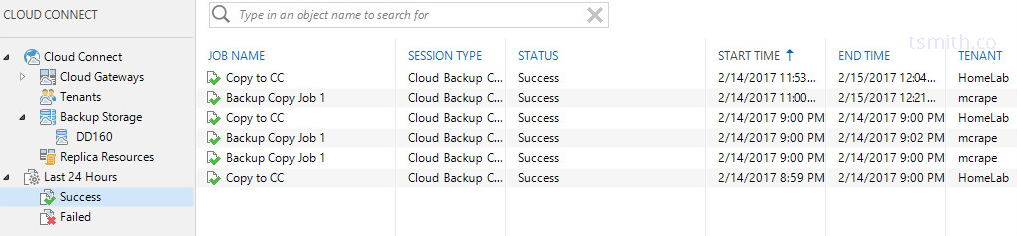
As a service provider, you can also monitor the jobs that are targeting the Cloud Connect environment, but for security purposes, the details will not be visible - only sucess and failure.
Setting up Cloud Connect from the Client Side:
 Be sure to follow along with fellow Veeam Vanguard
Matt Crape
in his post on how to connect a client Veeam Backup and Replication installation to a cloud provider
. Be sure to browse his blog for many other great Veeam related articles!
Be sure to follow along with fellow Veeam Vanguard
Matt Crape
in his post on how to connect a client Veeam Backup and Replication installation to a cloud provider
. Be sure to browse his blog for many other great Veeam related articles!